Online Proceedings
*Notice: PDF files are protected by password, please input "iPOP.19th-2023". Thank you.
Thursday 25, May 2023
iPOP Plenary
Thursday 25, May 2023, 10:00-12:20
Presider: Hiroaki Harai, NICT, Japan
Opening Address
Naoaki Yamanaka, General Co-Chair, Keio University, Japan
Bijan Jabbari, General Co-Chair, ISOCORE, USA
Bijan Jabbari, General Co-Chair, ISOCORE, USA
Keynote
Kenichiro Matsumoto, NTT, Japan

NTT launched the concept named IOWN(Innovative Optical and Wireless Network), an initiative for future communications infrastructure to create a smarter world by using cutting-edge technologies like photonics and computing technologies.
In order to realize this concept, we are collaborating with various partners in IGF(IOWN Global Forum) in parallel with research and development inside NTT R&D.
Many efforts toward practical implementation are underway through various experiments.
In this session, I will share the aim and the latest status toward the realization of the IOWN concept and also introduce the commercial services that have already started in this March.
Biography:
Kenichiro Matsumoto is the head of NTT Network Service Systems Laboratories.
Since he joined NTT in 1994, he was mainly engaged in research and development of large-scale network systems such as ATM switching systems and next-generation network (NGN) systems. He was also engaged in standardization activities for B-ISDN signaling in ITU-T. He was in charge of research and development of 5G core network architecture in NTT DOCOMO Core Network Development Department for two years from 2017. Since 2019 he has been engaged in research and development of transport network systems and core network technologies in NTT Network Service Systems Laboratories.
Emmanuel Le Taillandier de Gabory, NEC, Japan

In this keynote, we will present the sustaining demands and requirements for future networks,
which include ultra-high capacity and ultra-wide coverage, as well as the implied challenges.
We will review strong technological candidates and initiatives to meet these challenges for
optical and wireless networks. These will include wide band optical transmission and spatial
division multiplexing technologies, as well as novel management technologies to include them
in future networks. We will also present novel technologies to extend the coverage of wireless
networks, which will include novel MIMO technologies and integration of non-terrestrial
networks.
Biography:
Emmanuel Le Taillandier de Gabory was born in Libourne, France, in 1975. He received a
MSc from the École Supérieure d’Optique, Orsay, France, in 1999. From 2000 to 2007, he
worked with Fujitsu Quantum Device Ltd., Yamanashi, Japan. He was in charge of developing
tunable lasers and transceiver modules for optical communication. In 2007, he joined NEC
Corporation, Kanagawa, Japan, where he is currently a Director in the Advanced Network
Research Laboratories.
He has been working on transmission technologies for high-capacity long-haul WDM
transmission systems, also including SDM transmission systems. He contributed to the
world’s first demonstration of real-time single-carrier 100G transmission in 2010, to the
realization of best-in-class transpacific QAM systems in 2016, and to the realization of the
world first trial of submarine cable with multicore fiber. He has authored and coauthored more
than 80 papers and 30 patent applications. He is a senior member of the IEICE (Japan) and
has served as member of the several Technical Committees such as ECOC, OECC and EXAT.
iPOP Exhibition introduction
- iPOP Exhibition Co-Chair
Local Arrangement
- iPOP Local Arrangement Co-Chair
Technical Session
Tech. Session (1):
Thursday 25, May 2023, 13:30-15:10
Chair: Kozo Satoda, NEC, Japan
Masaki Kotoura and Masahiro Hayashi, Tokyo City University, Japan

The traditional approach to ensuring high security is encryption. However, some researchers have claimed that it is not so secure if the hardware is stolen, because the thieves can decrypt data in the hardware with sufficiently long days. The secret sharing scheme (SSS) is one way to prevent such hardware theft. This scheme divides data (called a ‘secret’) into several pieces (called ‘shares’) and delivers them to shareholders. Even if a share is stolen, hacker cannot decrypt it because they must aggregate several shares from different shareholders.
Visual secret sharing is one of influential scheme to realize SSS, because it can prevent robotically executed brute force attacks by requiring the use of the human eye. It uses several transparent sheets having meaningless split figure. A person cannot decrypt the secret from each sheet, but can decrypt it by visually superposing all the sheets.
While the visual secret scheme is considered useful, it still has a problem because decryption becomes difficult if we use sheets that have been repeatedly copied from the original sheet. Successive copies will have misalignments of the figures and the human eye cannot compensate for such misalignments.
We propose a new technique which is not a visual but rather a topological secret sharing scheme. The key idea is to use not a figure but rather a diagram, where the diagram is conceptual one and therefore the viewer can recover it more easily than a figure after misalignments caused by repeated copying. For example, readers will agree that a graph consisting nodes and links, which is a typical diagram, is tolerant to the sort of repeated copying that might change the left figure into the right one below.
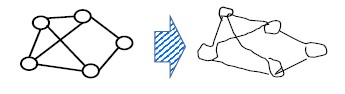
Fig.1
The procedure of the topological secret sharing scheme, where the secret is a number, is as follows.
- Select a problem to compute an index of a graph from its topology and the weights of its links.
- Construct a graph whose index is equivalent to the secret.
- Cut this graph into several pieces as shares.
We select the problem of computing the probability of two specified nodes being connected as the Basic Problem and demonstrate the effectiveness of our proposal by numerical examples in this case
Biography:
Masaki Kotoura was born in Wakayama, Japan in 2000. He received the bachelor’s degree from Tokyo City University in 2023. He is currently a master’s degree student in Major of Department of Information Security, Graduate School of Information Security, Institute of information security. His interest is security theory and its application.
Yutaro Suda and Masahiro Hayashi, Tokyo City University, Japan

Large and complicated computations in science and engineering are often outsourced
to subcontractors or to powerful supercomputers. However, outsourcing has a security
problem, because we must reveal important data, such as on customers or reliability of
equipment, to the subcontractors. Secure computation is a solution to this problem, and
fully homomorphic encryption (FHE) is one of its key technologies, realizing a secret
computation by using a mapping Ψ( ) having the following three properties, where x
and y are numbers.
,
,
is obtaned by security keys
The IH method is considered to be the only method among the various types of FHE
that is applicable to a computation involving real numbers expressed by long strings of
digits. We summarize it below.
Let f be a polynomial whose input variables are x1, x2, … , xn. The order m of f is
defined as the order of f|x1 = x2 = … = xn = x. For example, the order of f = (1 – x1)2x22 is 4
because f|x1 = x2 = x = x2 −2x3 + x4. 𝜑 h(f) is defined as
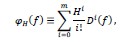
where D is a specific differential operator and H is a secret key. 𝜑H( ) satisfies the conditions of Ψ( ), and its decryption is executed by using a specific matrix M of size 'm+1'×'m+1'.
While the IH method is considered useful, it cannot be applied if f includes divisions, because m becomes infinite if f is not a polynomial.
Here, we propose a solution for this problem even in the case of f including divisions, by using the following facts.
- Any f defined above can be reduced to f1/f2, where f1 and f2 are each polynomials.
- Let m1 and m2 be the orders of f1 and f2, respectively. We can find an extended matrix M’ of size m+×m+, where m+ = Max(m1, m2) + 1 .
- The IH method can be applied by replacing m with Max(m1, m2) and M with M’.
Finally, we give numerical examples to show the effectiveness of our proposal.
Biography:
Yutaro Suda was born in Kanagawa, Japan in 2000. He received the bachelor’s degree from Tokyo City University in 2023. He is currently a master’s degree student in Major of Informatics, Graduate School of Integrative Science and Engineering, Tokyo City University. His interest includes security theory and its application.
T1-3
"Dynamic task assignment experiment for container-based in-network heterogeneous distributed MEC environment"
Koki Muramatsu, Masaki Murakami, Yoshihiko Uematsu, Satoru Okamoto, and Naoaki Yamanaka, Keio University, Japan

We have proposed AMec (Access-metro Edge Computing), a concept of edge computing that uses surplus in-network computing resources such as CPUs on network devices [1]. As targets of computing resources, we first assume CPUs on network devices (routers, switches, ROADMs, etc.) owned by telecommunication carriers, and in the future, we are also considering utilizing underutilized home game consoles and IoT devices.
Last year, as in the iPOP showcase, we managed servers by OpenStack and connected them to ARCA[2]. We showed a virtual machine on a server provided by ARCA initialized and automatically attended to AMec cluster and was assigned some tasks by the AMec controller. This means that the AMec concept was shown on the homogeneous x86 CPU-based virtual machine environment, not on in-network device (emulated) environment.
This year, to approach the concept described above, we have challenged to use Kubernetes and make a cluster consisting of heterogeneous resources which will emulate in-network devices, and multiple container-based applications will run on them. This allows AMec worker to execute multiple application by downloading container image from library such as Docker-Hub.
Because of utilizing surplus computing resources, AMec cannot always occupy them for AMec tasks. For example, there are times when resources on network devices are reclaimed for their original tasks, such as information gathering and routing reconfiguration, and then are not available for AMec tasks.
To solve this problem, we plan to implement a system in which each network device detects its resource availability and automatically joins the AMec cluster. AMec controller receives requests from AMec workers to join the cluster and mediates them.
In addition, we are going to work on the following issues.
- Container migration in case resources become unavailable or to follow the users’ hand-over
- Predict the resource available duration on each device and judge what kind of container the device is suitable for
- Optimization of application container placement based on above two
In my presentation, some experimental results will be shown.

Acknowledgment:
This work is also partly supported by the R&D of innovative optical network technologies for supporting new social infrastructure project (JMPI00316) funded by the Ministry of Internal Affairs and Communications Japan.
Reference:
- S. Okamoto, K. Sugiura, M. Murakami, and N. Yamanaka, "Proposal of Block-stream as a Service-based Access-Metro Edge Computing Technologies", Program of the 2020 IEICE Society Conference, 2020.
- P. Martinez-Julia, V. P. Kafle and H. Harai, "Exploiting External Events for Resource Adaptation in Virtual Computer and Network Systems," in IEEE Transactions on Network and Service Management, vol. 15, no. 2, pp. 555-566, June 2018
Biography:
Koki Muramatsu received his B.E. degree from Keio University in 2022. He is currently a master course student in Graduate School of Science and Technology, Keio University.
Cengiz Alaettinoglu, Ciena, USA

Synopsis:
When an IP network is congested, operators could take advantage of the channel margins in the underlying optical network and increase capacity of the IP links. Although channel margins are required for the long-term health of the optical service, it might be possible to tap into the margin while the IP network is being repaired. We present a new converged Traffic Engineering SDN approach that looks at the IP and optical layers of the network holistically to help operators alleviate IP congestion.
Description:
The talk is about multi-layer optimization using SDN control. We give a brief description of the Shannon channel capacity law and optical margins and how these margins can be mined for additional capacity using streaming telemetry and machine learning. We then illustrate IP layer congestion caused by an optical fiber cut. Conditions are such that congestion cannot be alleviated, neither by using IP traffic engineering alone, nor by using optical restoration alone. However, a solution using a coordinated optimization is possible. Indeed, we show 3 solutions to the problem using partial capacity optical restoration and IP traffic engineering, borrowing from margins and IP traffic engineering, and by introducing a new express link to the IP topology and IP traffic engineering. The key take away is that the process is too complicated to be done by operators manually and can only be realized by software SDN control. The presentation is based on a talk I gave at NANOG February 2023. I would like to extend on the transitional link flexibility and cost of change contents for iPoP 2023.
Biography:
Cengiz Alaettinoglu is a Ciena Fellow and is responsible for the technical direction and architecture of Ciena’s MCP Applications portfolio. He is currently focused on multi-layer network automation.
Before joining Ciena through the Packet Design acquisition in 2018, Cengiz lead development of real-time SDN analytics and orchestration applications which intelligently adapt paths based on changing network conditions, using intent-based policies and real-time analytics. His early experimental work, correlating network performance issues to routing protocol incidents, pioneered the use of analytics in IP network routing. Prior to Packet Design, Cengiz was with USC's Information Sciences Institute where he worked on the Routing Arbiter project. He was co-chair of the IETF's Routing Policy System Working Group, has been published widely, and is a popular presenter at industry events worldwide.
Cengiz holds a BS in Computer Engineering from Middle East Technical University, Ankara, and a MS and PhD in Computer Science from the University of Maryland.
Tech. Session (2):
Thursday 26, May 2023, 16:00-17:10
Chair: Kiyoshi Onohara, Mitsubishi Electric, Japan
Daisuke Hasegawa and Masahiro Hayashi, Tokyo City University, Japan

We focus on the rounding error problem in computing network reliability (the probability of network being in the working state, denoted by R) from component (cable, router, or other equipment) reliabilities denoted by R1, R2, … , Rn, which is a significant issue in the QoS research field.
Traditional solutions to the rounding error problem are based on Moor’s approach, which gives lower and upper approximations. However, we claim this because Moor’s approach gives different bounds depending the algorithms to be computed.
We give a specific solution for computing R.
The key idea is explained below.
For example, if R={1-(1-R1)(1-R2)}R3 with R1=R2=R3=0.9 and T=0.1, then R=[1-{1-(1-0.1)}{1-(1-0.1)}](1-0.1)}=[1-{1-(1-T)}{1-(1-T)}](1-T)=1-T-T2+T3, where we use only integer calculations in deriving 1-T-T2+T3.
We can compute the exact value of R as 1-0.1-0.12+0.13=0.891 from this. That is, we can avoid the rounding error.
R= f(T) ≡C0+C1T+C2T2+ … +CnTn, (1)
where C1, C2, … , Cn are integers. By comparing Eq.(1) with the Maclaurin expansion,
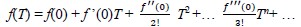
we find that ]
Fortunately, the method of ref. [1] enables us to determine all 𝑓(𝑘)(0)/𝑘! terms with polynomial-time-order as for n after obtaining f(T).
We emphasize that we can compute the lower and the upper bounds of R by ignoring high-order terms in f(T), while these bounds never depend on the algorithms used to compute R.
Finally, we demonstrate numerical examples to show the effectiveness of our proposal.
References:
- D. Kalman et al., “Combinatorial and functional identities in one-parameter matrices”, The American Mathematical Monthly, vol. 94, no. 1, pp. 21-35, 1987.
Biography:
Daisuke Hasegawa was born in Tokyo, Japan in 1999. He received the bachelor’s degree from Tokyo City University in 2023. He is currently a master’s degree student in Major of Information Engineering, Tokyo City University. His research focuses on reliability evaluation methods for telecommunications networks.
Taichi Soma and Masahiro Hayashi, Tokyo City University, Japan

How to realize reliable communications networks is a significant issue, and reliability importance analysis gives us an effective methodology for this. The Birnbaum importance, which is an index used in this analysis, is defined as the first-order partial derivative of reliability (the probability of the network being in a working state) of the network with respect to the reliability of the component (cable, router, or other equipment). It clarifies which component should be improved with high priority under the limitation of a budget. The joint reliability importance is another index, defined as second-order partial derivative. It clarifies the correlation between the improvements in the reliabilities of the two components as to whether there is a synergy, diminishing returns, or no correlation. Furthermore, the k-th order joint reliability importance is defined as the k-th order partial derivative of the network reliability, where it clarifies the resilience of the Birnbaum and joint reliability importances.
While the k-th order joint reliability importance is considered to be useful, the computation time of the existing method of determining it increases exponentially as k increases.
This presentation shows a new method to avoid this exponential increase.
We find
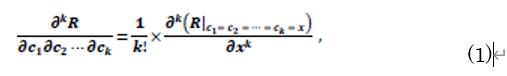
where R denotes the reliability of the network, and c1, c2, … , ck ∈{R1, R2, …, Rn}, with R1, R2, …, Rn being the reliabilities of the components. For example, if R = R1R2 + R3R4 – R1R2R3R4 with c1 = R1, c2 = R2, c3 = R4, and k = 3, then elementary techniques to compute partial derivative show that the l. h. s. of Eq. (1) equals – R3 and we can find the same result from the r. h. s. of Eq. (1) as follows.
Fortunately, the r. h. s. of Eq. (1) can be computed with polynomial order by using the technique of ref. [1]. Finally, numerical examples are demonstrated to show the effectiveness of our proposal.
- D. Kalman and A. Unger, "Combinatorial and functional identities in one-parameter matrices", The American Mathematical Monthly, vol. 94, no. 1, pp. 21-35, 1987.
Biography:
Taichi Soma was born in Chiba, Japan in 1999. He received the bachelor’s degree from Tokyo City University in 2023. He is currently a master’s degree student in Major of Informatics, Graduate School of Integrative Science and Engineering, Tokyo City University. His research focuses on reliability evaluation methods for telecommunications networks.
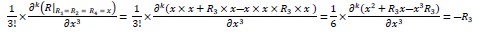
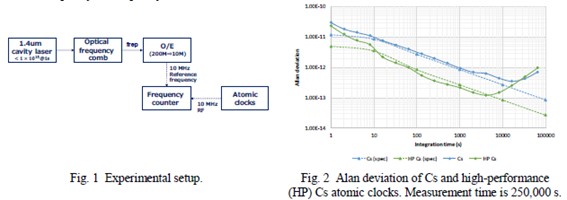
Kota Nishiyama, Kaoru Arai, Ryuta Sugiyama, Hiromitsu Imai, Kenichi Hitachi,Tomoya Akatsuka, Katsuya Oguri, and Takashi Miyamura, NTT, Japan

Optical clocks are attracting a great deal of attention as a next generation frequency standard. A major feature of optical clocks is that the frequency reference is the optical frequency, as opposed to the frequency of conventional microwave-based atomic clocks.
We are now considering supplying high-precision frequencies over all-photonics network with a high compatibility with optical frequencies, and utilizing the high-precision frequencies for reference frequencies for measurement or frequency synchronization. By using the high-precision optical reference frequency, absolute evaluation of the commercial atomic clocks frequency can be performed.
In this study, we propose using an optical frequency comb to obtain the reference radio frequency guaranteed by the optical reference frequency stability. An optical frequency comb is an optical device that can oscillate equally spaced optical pulses. By copying the high-precision optical reference frequency into the optical frequency comb, an optical pulse repetition frequency of the optical frequency comb with the same stability is expected to be obtained. However, there has been no report on the use of the radio frequency from an optical frequency comb as a reference frequency for frequency measurement of a high-precision frequency oscillator.
Figure 1 shows an experimental setup. Here, we synchronized an optical frequency comb with a high-precision optical laser at the wavelength of λ=1.4 μm as an optical reference frequency. This optical laser has a frequency instability of less than 1 × 10−15 for 1 second averaging time. Converting the repetition frequencies of the optical frequency comb into a radio frequency of 10 MHz, we could acquire an extremely stabilized reference frequency. We evaluated the frequency stability of frequency oscillation devices such as commercial Cs atomic clocks by comparing the frequency of the atomic clocks with the radio frequency from the optical frequency comb. As shown in Fig. 2, up to about 10,000 s integration time, we could measure the Allan deviation of the atomic clocks equivalent to the spec value, whereas more than 10000 s integration time, the measured values tended to rise above the spec values. This result is attributed to the fact that the optical cavity laser has a drift of about 10 mHz/s. By stabilizing the optical cavity laser with an optical clock, we would surely eliminate the frequency drift. This result showed that an optical frequency comb synchronized with high-precision optical reference frequency could potentially become a next-generation reference frequency for frequency evaluation.
References:
- K. Arai et al., "Study on High-Accuracy Synchronization System Using Optical Frequency Comb," IEICE General Conference, B-12, Feb. 2021 (in Japanese).
- T. M. Fortier et al., "Generation of ultrastable microwaves via optical frequency division," Nature Photon., vol. 5, pp. 425-429, 2011.
Biography:
Kota Nishiyama is a researcher with 3 years of experience researching on optical transmission network. He graduated from Keio university in 2020 with master degree in Applied Physics and Physico-Informatics. Now, he is specifically engaged in research about optical clock networks belonging to NTT Network Service Systems Laboratories and NTT Basic Research Laboratories.
Friday 26, May 2023
Technical Session
Tech. Session (3):
Friday 26, May 2023, 9:30-10:45
Chair: Eiji Oki, Kyoto University, Japan
Hanami Yokoi, Kohjun Koshiji, Tatsuya Matsukawa and Takashi Miyamura, NTT, Japan

I. INTRODUCTION
When a failure occurs in an optical network, the optical paths that pass through the network failure point are disabled. In such cases, it is desirable to rescue the optical paths that have become unavailable by redesigning them. However, if optical paths are redesigned in accordance with the usual design policy, the utilization of optical paths will be concentrated on some links, resulting in unbalanced resource utilization. When no spectrum resources are available in the routing link due to unbalanced spectrum resource utilization, the optical path cannot be accommodated. In this paper, we propose an optical path redesign method that reduces spectrum resource unbalance in order to accommodate a new optical path during a network failure. We focus on the requirements (attributes) of the communication demand in the optical path.
II. PROPOSED METHOD
As shown in Figure 1, the proposed method classifies optical paths into six types. Specifically, attribute 1 (low-latency with narrowband), attribute 2 (low-latency with wideband), and attribute 3 (ultra-wideband with no latency requirement) are defined on the basis of the use cases assumed in the IOWN Global Forum [1]. The optical paths that have been disconnected due to a fault are classified as attributes 1,2, and 3, and those that have not are classified as attributes 4, 5, and 6. The method consists of three steps.
- For attributes 1 and 2, redesign the shortest path and first-fit path from the path with the highest hop count.
- For attribute 3, redesign the path with the K-shortest path and First-Fit from the path with the largest number of hops.
- For attribute 6, redesign with K-shortest Path and First-Fit, starting from the path with the maximum spectrum slot number.
This method satisfies the requirements of optical paths and accommodates many optical paths in a network failure.
III. NUMERICAL EXAMPLES
In this section, we evaluate the performance of the proposed method in a simulation. Figure 2(a) shows the conventional method using the shortest path and First-Fit, which is the current basic policy for optical path design, and Figure 2(b) shows the proposed method. Figure 2(a) shows that the maximum spectrum slot number increases by up to 24% when a failure occurs on any link in JPN12 [2], compared with the value before the failure (blue). On the other hand, Figure 2(b) shows that the proposed method can reduce the maximum spectrum slot number by up to 15%. This result indicates that the proposed method can accommodate more optical paths even during a network failure.
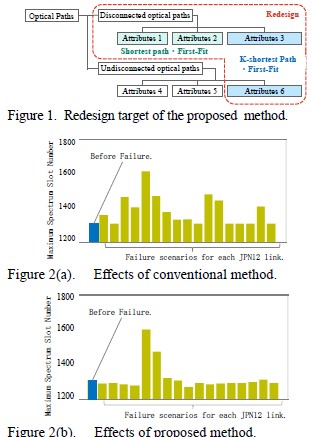
IV. CONCLUSION
In this paper, we proposed an optical path redesign method that takes into account the attributes of optical paths during network failures.
References:
- IOWN Global Forum System and Technology Outlook, https://iowngf.org/wp-content/uploads/formidable/21/IOWN-GF-RD-System_and_Technology_Outlook_1.0-1.pdf (accessed 2023-03-10)
- "Japan Photonic Network Model," Available online at: http://www.ieice.org/cs/pn/jpn/jpnm_e.html
Biography:
Hanami Yokoi received the B. Eng. degree from the Faculty of Engineering, University of Fukui, Japan, in 2018. She received the M. Eng. degree from the Graduate School of Engineering, University of Fukui, Japan, in 2020. She joined NTT Network Technology Laboratories in 2020. Currently, she is working on optical path design at NTT Network Service Systems Laboratories.
T3-2
"Spectral Grooming Strategies in Spatial Channel Network Based on WDM/SDM Hierarchical Optical Cross-Connects"
Koki Miura, Kako Matsumoto, Yudai Uchida, and Masahiko Jinno, Kagawa University, Japan

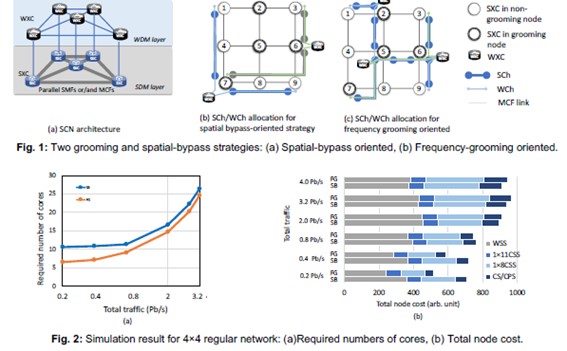
To accommodate future Internet traffic in a scalable and economical manner, the scalable and cost-effective spatial channel network (SCN) architecture has recently been proposed [1], where the current optical layer evolves into wavelength division multiplexing (WDM) and space division multiplexing (SDM) layers, and an optical node is decoupled into a spatial crossconnect (SXC) and a wavelength cross-connect (WXC) to form a hierarchical optical cross-connect (HOXC). SXCs and WXCs establish a spatial channel (SCh) and a wavelength channel (WCh), which are media channels in the SDM and WDM layers, respectively.
In order to take full advantage of hierarchical grooming in SCNs, it is important to develop efficient routing and spectrum and core assignment (RSCA) algorithms [2. 3] that balance the efficiency of network resource (spectrum and core) utilization and the cost-effectiveness of HOXC deployment. In this paper, we compare two spectral grooming strategies for a local traffic in an RSCA algorithm: (a) Spatial-bypass oriented (SB), (b) Frequency-grooming oriented (FG). Here, a local traffic is a nonexpress traffic, which is carried while sharing SChs on the route with other local traffic having different source/destination pairs by being spectrally groomed in WXCs. Figure 1 illustrates how each traffic demand is accommodated to a WCh and SCh(s), and how a WXC is deployed, for each of the strategies employed. Hear, circles represent SXCs, of which the doubleline circles represent SXCs where WXCs can be deployed (this node is referred to as the grooming node). The FG strategy attempts to use core resources efficiently and select SCh that pass through more frequency grooming nodes. The SB strategy, on the other hand, attempts to accommodate demand using as few SCh as possible to reduce the number of WXCs. There is a trade-off between the number of cores and the number of WXCs required. Figure 2 is an example of simulation results for a 4×4 regular network based on an RSCA algorithm reported in [2. 3], which shows that the FG strategy requires fewer cores and lower node cost than the SB strategy in the low-traffic region, but in the high-traffic region, the node cost of the SB strategy becomes lower than that of the FG strategy, and the number of cores required becomes almost equal. Simulation results for different network topologies will be presented at the conference.
Acknowledgment:
This work was supported in part by the JSPS KAKENHI (JP22H01488) and the NICT (00201).
References:
- M. Jinno, "Spatial channel network (SCN): Opportunities and challenges of introducing spatial bypass toward massive SDM era," J. Opt. Commun. Netw., 11, 3, pp. 1-14, 2019.
- M. Jinno, Y. Asano, Y. Azuma, T. Kodama, and R. Nakai, "Technoeconomic analysis of spatial channel networks (SCNs): Benefits from spatial bypass and spectral grooming," Journal of Optical Communications and Networking, vol. 13, no. 2, pp. A124-A134, 2021.
- K. Matsumoto, K. Miura, Y. Uchida, and M. Jinno, "Impact of connection flexibility in spatial cross-connect on core resource Utilization efficiency and node cost in spatial channel networks" ECOC 2022, Tu5.43.
Biography:
Koki Miura received the B.E. degree in electronics and information engineering from Kagawa University, Takamatsu, Japan in 2023. He is currently a graduate student at Kagawa University and a Student Member of the Institute of Electronics, Information and Communication Engineers (IEICE).
Kana Masumoto, Masahiro Nakagawa, Toshiya Matsuda, Kota Nishiyama, Takeshi Seki, Takashi Miyamura, NTT, Japan

Optical time division multiplexing (TDM) is investigated by applying it to aggregation metro networks because it enables low cost and low consumption by reducing the number of routers and transponders [1]-[4]. However, current metro networks are composed of reconfigurable optical add-drop multiplexer (ROADM) networks, and their configuration is expected not to change in the future. Therefore, Optical TDM is expected to be applied to ROADM networks when Optical TDM is applied to metro networks. [1]-[4] did not sufficiently discuss node configurations when Optical TDM is applied to ROADM networks because they did not consider the above facts. Optical TDM networks have a problem that they cannot provide sufficient transmission distance on metro networks depending on node configurations and used devices because they are composed of passive devices (ex. Optical couplers) [5].
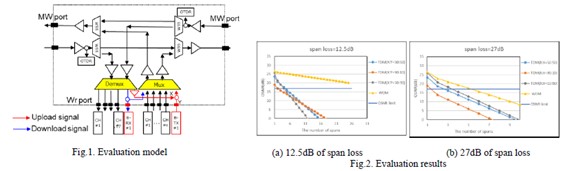
Therefore, a node configuration is used that applies optical TDM to ROADM networks using Open ROADM MSA, and its transmission performance is evaluated by using the optical signal-to-noise ratio (ONSR) while changing the span loss and branching ratio of an optical coupler. Fig.1 shows the evaluation model. X:Y of branching ratio is 50:50, 90:90, and 10:90. Span losses are 12.5 dB (25 km) and 27dB (54 km), which assume the use of 0.5 dB/km single-mode fiber (SMF). The OSNR limit is set to 17 dB [6]. The transmission at the evaluating span succeeds when the OSNR exceeds 17 dB. For a comparison, transmission performance is evaluated by using wavelength division multiplexing (WDM) signals as well.
Figs. 2(a) and 2(b) show the evaluation results. Fig. 2(a) shows the Optical TDM signal achieves 4, 1, 3 transmission spans when the branching ratios are 50:50, 90:90, 10:90 while WDM signal achieves over 25 transmission spans. Fig. 2(b) shows the Optical TDM signal achieves 2, 1, 3 transmission spans when branching ratios are 50:50, 90:90, 10:90, while WDM signal achieves 5 transmission spans. The Optical TDM signal limits transmission distance because OSNR of Optical TDM signals degrade largely compared with WDM signal. Thus, the Optical TDM signal cannot achieve a sufficient transmission distance on metro networks.
Therefore, transmission distance is evaluated quantitatively, and the issues of this node configuration are clarified by evaluating transmission performance Optical TDM in ROADM networks. A sufficient transmission distance is expected to be achieved by adding an amplifier, increasing the transceiver output power, and so on. We are going to evaluate that in the future.
References:
- D. Amar et al., ICTON 2017.
- B. Han et al., J. Light. Technol., Vol. 39, Issue 6, 15 Mar. 15th, 2021
- N. Benzaoui et al., PSC2019
- B. Pan et al., J. Light. Technol., Vol. 40, Issue 8, Apr. 15th, 2022
- M. Nakagawa et al., ONDM 2018
- open-roadm_msa_specification_ver5.0
Biography:
Kana Masumoto received her B.E., M.E. degrees from Waseda University in 2013, 2015, respectively. She joined the Nippon Telegraph and Telephone Corporation (NTT) in 2015. Since then, she has been involved in research of the optical transmission system, especially optical TDM networks and Innovative Optical and Wireless Network All Photonics Network (IOWN APN).
Sponsor Session
Friday 26, May 2023, 11:00-11:40
Chair: Takaya Miyazawa, NICT, Japan
Kenta Hirose, NTT , Japan
Biography:
Kenta Hirose received a B.E. in applied physics and M.E. in materials science from Keio University, Kanagawa, in 2017 and 2019. He joined NTT Network Service Systems Laboratories in 2019 and has been researching multiband optical transmission technologies. He is also developing optical transmission systems at NTT Network Innovation Center.
Shinya Nakamura, UBiqube (Ireland) Limited , Ireland

Biography:
SHINYA NAKAMURA received his B.E. and M.E degrees in Electrical Engineering and Electronics from the Aoyama Gakuin University (Tokyo Japan) in 1981 and 1983, respectively.
Currently, he leads UBiqube’s APAC region Business Development focusing Integration and Automation for the heterogeneous multi-vendor/multi-domain infrastructure and hybrid cloud environments. He has more than 35 years of experience in Global Telecommunication industry and has published more than 40 technical papers and contributions to standardization organization, taken part of telecommunications conferences and symposiums as session chairman, technical committee member or invited speaker. He is a member of the IEEE Communications Society.
Special Panel Session
Friday 26, May 2023, 13:00-14:30
Special Panel Session
Theme: "Network Security toward Beyond 5G era"
Moderator:
Norihito Fujita, NEC, Japan

Panelists:
- Yoshiaki Nakajima, NTT, Japan

- Ayumu Kubota, KDDI Research, Japan

- Katsunari Yoshioka, Institute of Advanced Sciences Yokohama National University, Japan

- Shoji Temma, Fujitsu, Japan


Theme: "Network Security toward Beyond 5G era"
Moderator:
Norihito Fujita, NEC, Japan

Biography:
Norihito Fujita reveived the B.E. and M.E. degrees in electrical engineering from Kyoto University, Japan, in 1996 and 1998, respectively. He joined NEC Corporation in 1998 and is a General Manager at Secure System Research Laboratories, NEC Corporation. He was a visiting researcher at the Univ. of Sauthern California/Information Sciences Institute from 2004 to 2005. His research interests includes control of network systems and security in critical infrastructure.
Panelists:
- Yoshiaki Nakajima, NTT, Japan

Theme:"The Importance of Security Transparency in Networks"
Biography:
Yoshiaki Nakajima, Executive Research Engineer in NTT Social Informatics Laboratories. He received M.S. in mathematical and computing science from Tokyo Institute of Technology in 1997. He joined NTT Information and Communication Systems Laboratories in 1997. He has been involved in research and development of information and communication platforms, security platforms, and other areas. He has certifications of Certified Information Systems Security Professional (CISSP), Certified Cloud Security Professional (CCSP), and Registered Information Security Specialist (RISS).
- Ayumu Kubota, KDDI Research, Japan

Theme:"Security Considerations for 5G/B5G Networks"
Biography:
Ayumu Kubota received the B.E. and M.E degrees of information engineering from Kyoto University, Japan, in 1993 and 1995, respectively. He joined KDD (now KDDI) in 1995, and has been engaged in the research on IP network and cyber security. He is now leading Cyber Security Laboratory in KDDI Research Inc.
- Katsunari Yoshioka, Institute of Advanced Sciences Yokohama National University, Japan

Theme:"IoT Cyber-attacks: Now and Future"
Biography:
Katsunari Yoshioka received his Ph.D. in Computer Engineering from Yokohama National University in 2005. From 2005 to 2007, he was a Researcher at the National Institute of Information and Communications Technology in Japan. He is a Professor at the Graduate School of Environment and Information Sciences, Yokohama National University. His research interest covers a wide range of information security, including malware analysis, network monitoring, intrusion detection, etc.
- Shoji Temma, Fujitsu, Japan

Theme:"Network connection control for trusted data exchange"
Biography:
Shoji Temma, Principal Engineer in Fujitsu. He received M.S. degree in system and information from Hiroshima University in 1983. He started work for product development for fault-tolerant server, cryptography accelerator, network server integrating load balancer and security functions in Fujitsu Limited from 1983. He also developed network system for Fujitsu cloud service. He is interest in CPS/IoT architecture and trust data distribution architecture. He had activities in IIC and OpenFog Consortium, and in OpenFog Consortium, He was a technical reader in Japan Region. He worked for trust data distribution network system in a national project SIP (Cross-ministerial Strategic Innovation Promotion Program)
Invited Session
Friday 26, May 2023, 15:00-16:00
Chair: Takehiro Tsuritani, KDDI Research, Japan
Diego R. Lopez,Telefonica, Spain

In the last decade, networks are being built on many principles set by the current practices in cloud infrastructures. This transformation approach implies great opportunities in terms of sustainability, agility, usability, etc. but we cannot forget the requirements of network services go beyond, and many times in different directions, than what cloud practice can provide. This talk will discuss the main technology solutions and challenges in this transformation enterprise.
Biography:
Dr Diego R. Lopez joined Telefonica I+D in 2011 as a Senior Technology
Expert, and is currently in charge of the Technology Exploration
activities within the GCTIO Unit. Before joining Telefónica he spent
some years in the academic sector, dedicated to research on network
services, and was appointed member of the High-Level Expert Group on
Scientific Data Infrastructures by the European Commission.
Diego is currently focused on applied research in network
infrastructures, with a special emphasis on virtualization, data-driven
management, new architectures, security, and quantum communications.
Diego is an ETSI Fellow and chairs the ETSI ISGs ZSM (on network
automation) and the NOC of ETSI ISG NFV.
Closing Session
Friday 26, May 2023, 16:00-16:20
Closing by iPOP Organization Committee Co-Chair
Satoru Okamoto,Keio University, Japan
Closing by iPOP Organization Committee Co-Chair
Satoru Okamoto,Keio University, Japan